Tryout Flow
This document provides step by step instructions to deploy, subscribe, and invoke the Account and Transaction API.
Tip
When the TPP provides an Account Information Service as an online service, the TPP is known as an Account Information Services Provider (AISP).
Deploying Account and Transaction API¶
-
Sign in to the API Publisher Portal with the credentials for
[email protected].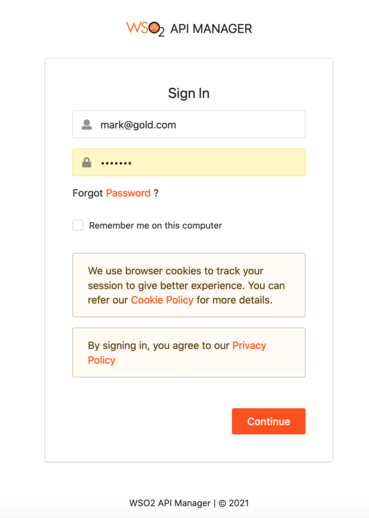
-
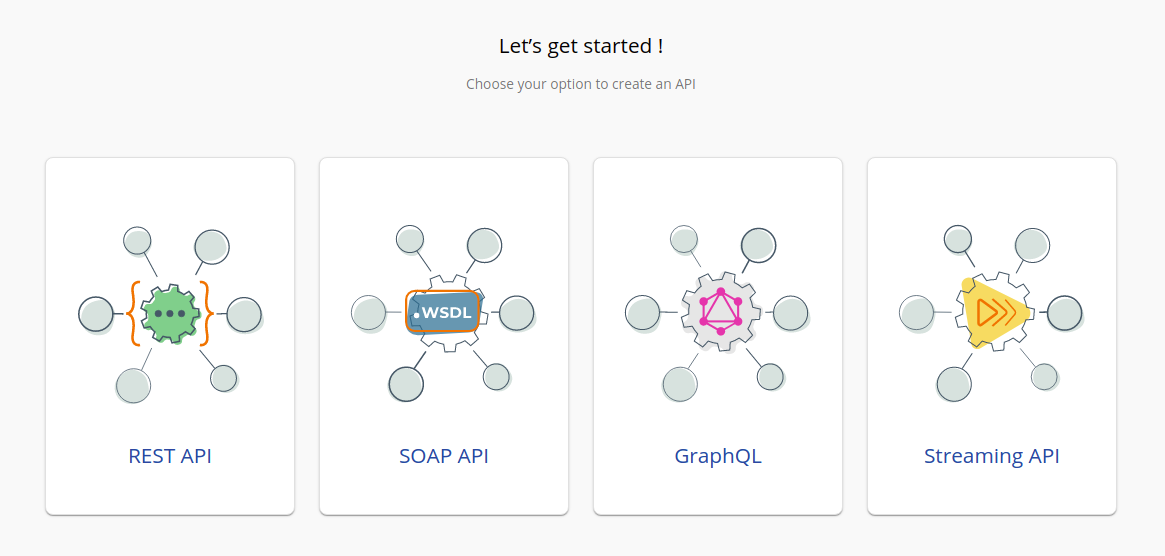
In the homepage, go to REST API and select Import Open API.
-
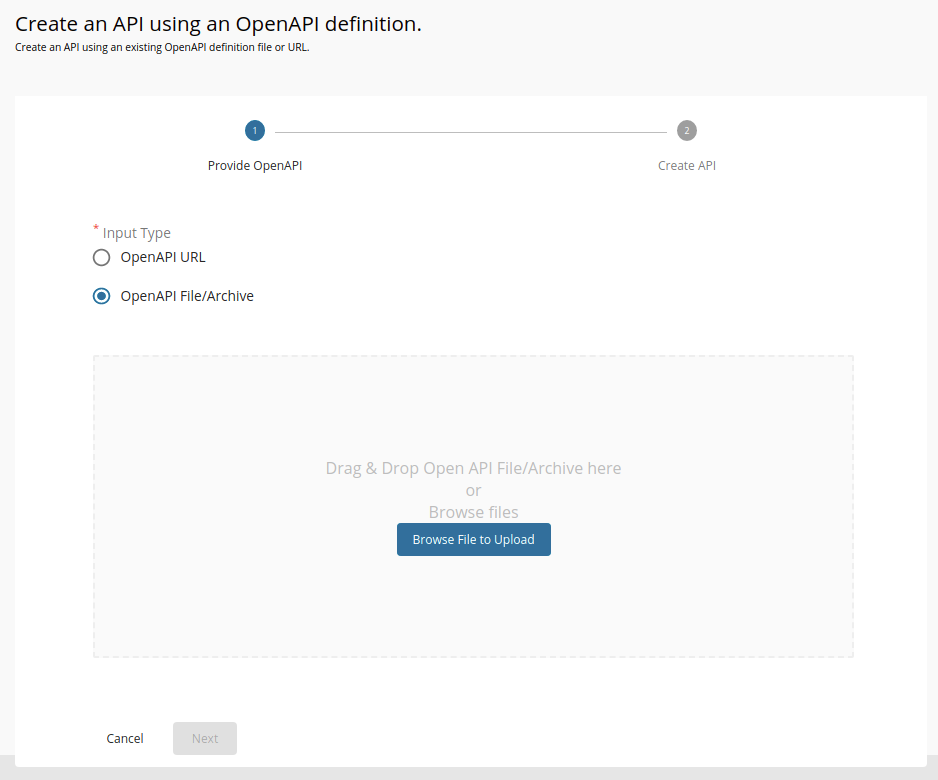
Select OpenAPI File/Archive.
-
Click Browse File to Upload and select the relevant API from the
<APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/Accountsdirectory. -
Click Next.
-
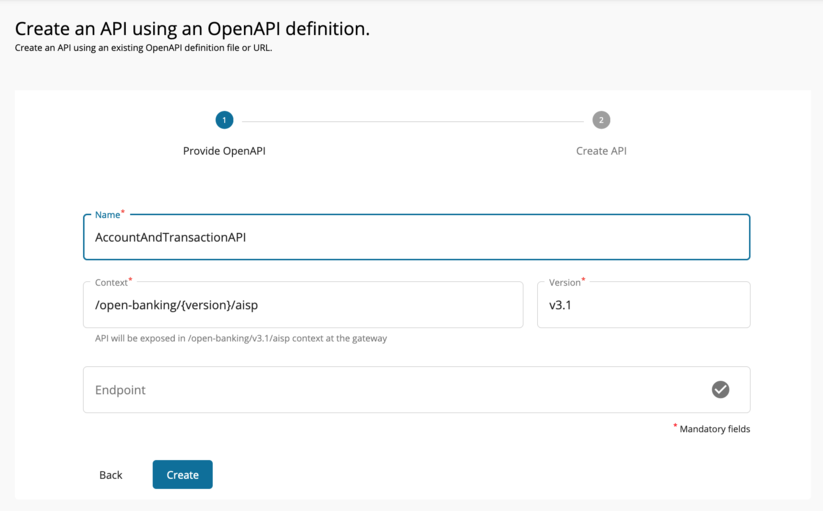
Set the Context value as follows:
/open-banking/{version}/aispAnd set the version as
v3.1if you are using API version 3, For API version 4 usev4.0 -
Click Create to create the API.
-
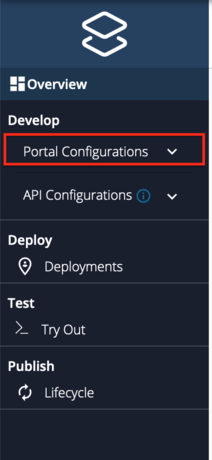
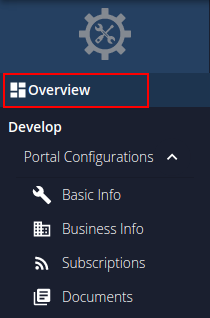
After the API is successfully created, go to Portal Configurations using the left menu panel.
-
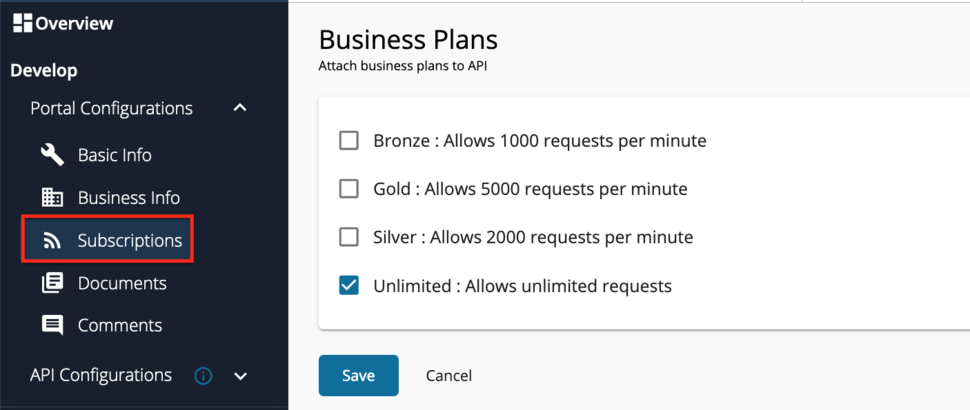
Select Subscriptions from the left menu pane and set the business plan to Unlimited: Allows unlimited requests.
-
Click Save.
-
Go to Runtime using the left menu pane.
-
Toggle the Schema Validation button to enable Schema Validation for all APIs except for the Dynamic Client Registration API.

-
Add a custom policy. Follow the instructions given below according to the API Manager version you are using:
Click here to see how to add a custom policy if you are using API Manager 4.0.0...
-
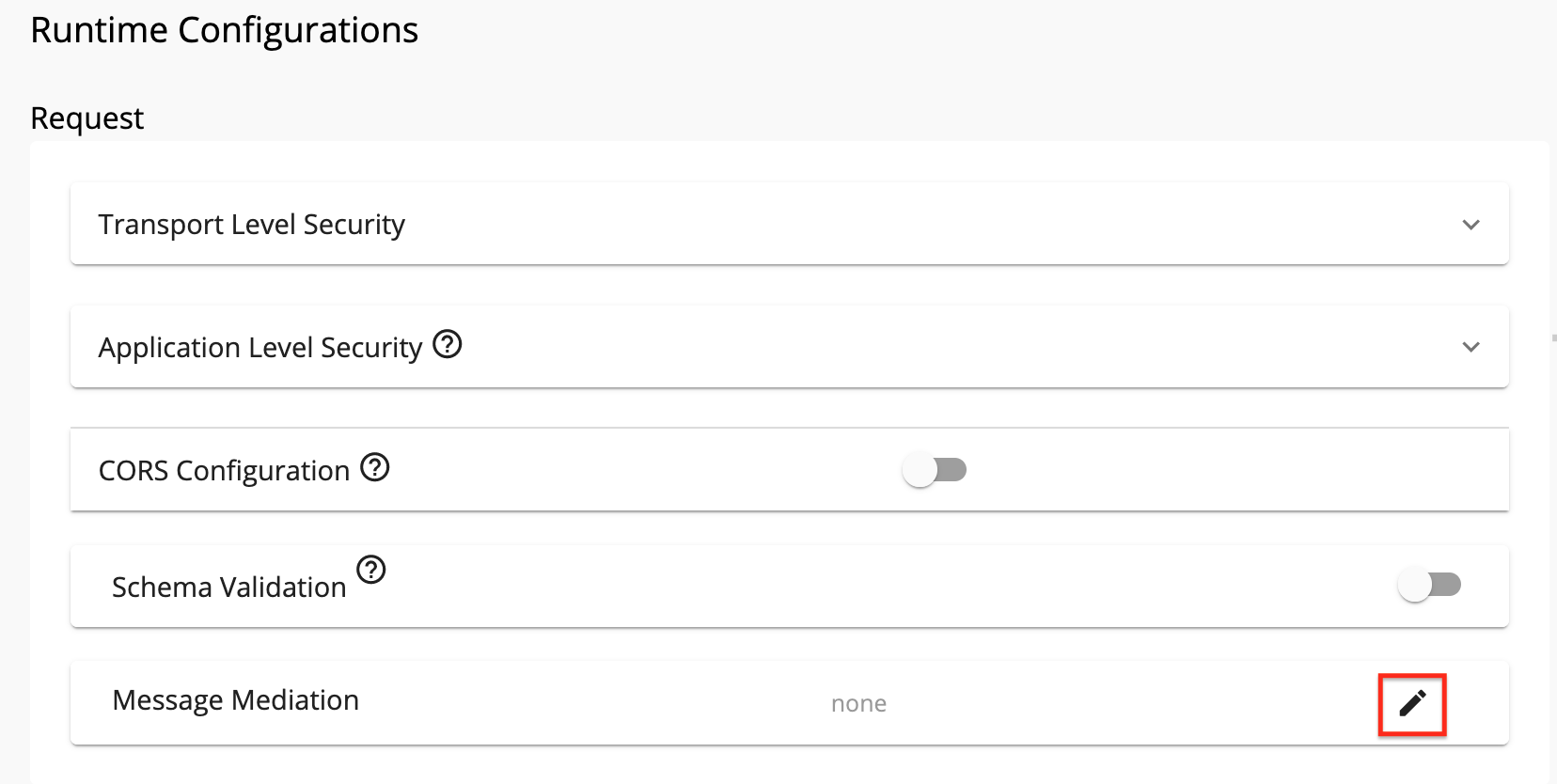
Click the Edit button under Request > Message Mediation.
-
Select the Custom Policy option.
-
Upload the relevant insequence file from the
<APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/Accountsdirectory.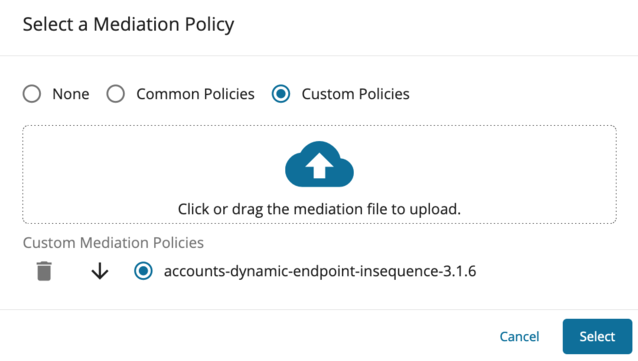
-
Click Select.
-
Scroll down and click SAVE.
Click here to see how to add a custom policy if you are using API Manager 4.1.0 or 4.2.0...
-
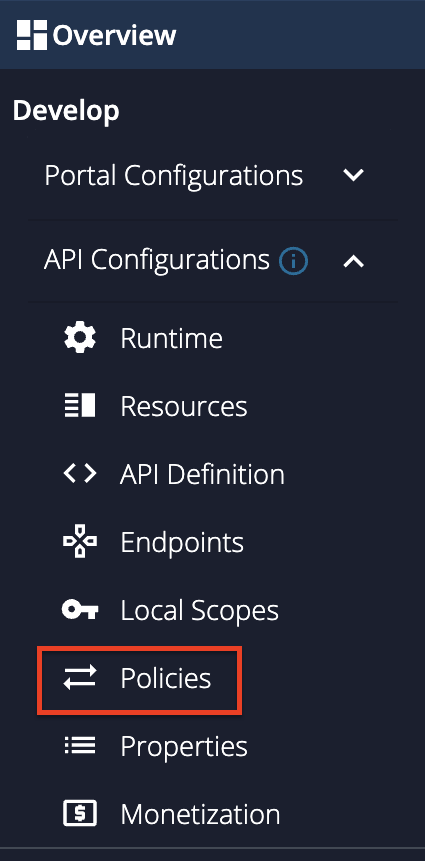
Go to Develop -> API Configurations -> Policies in the left menu pane.
-
On the Policy List card, click on Add New Policy.
-
Fill in the Create New Policy.
-
Upload the relevant insequence file from the
<APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/Accountsdirectory. -
Scroll down and click Save. Upon successful creation of the policy, you receive an alert as shown below:

-
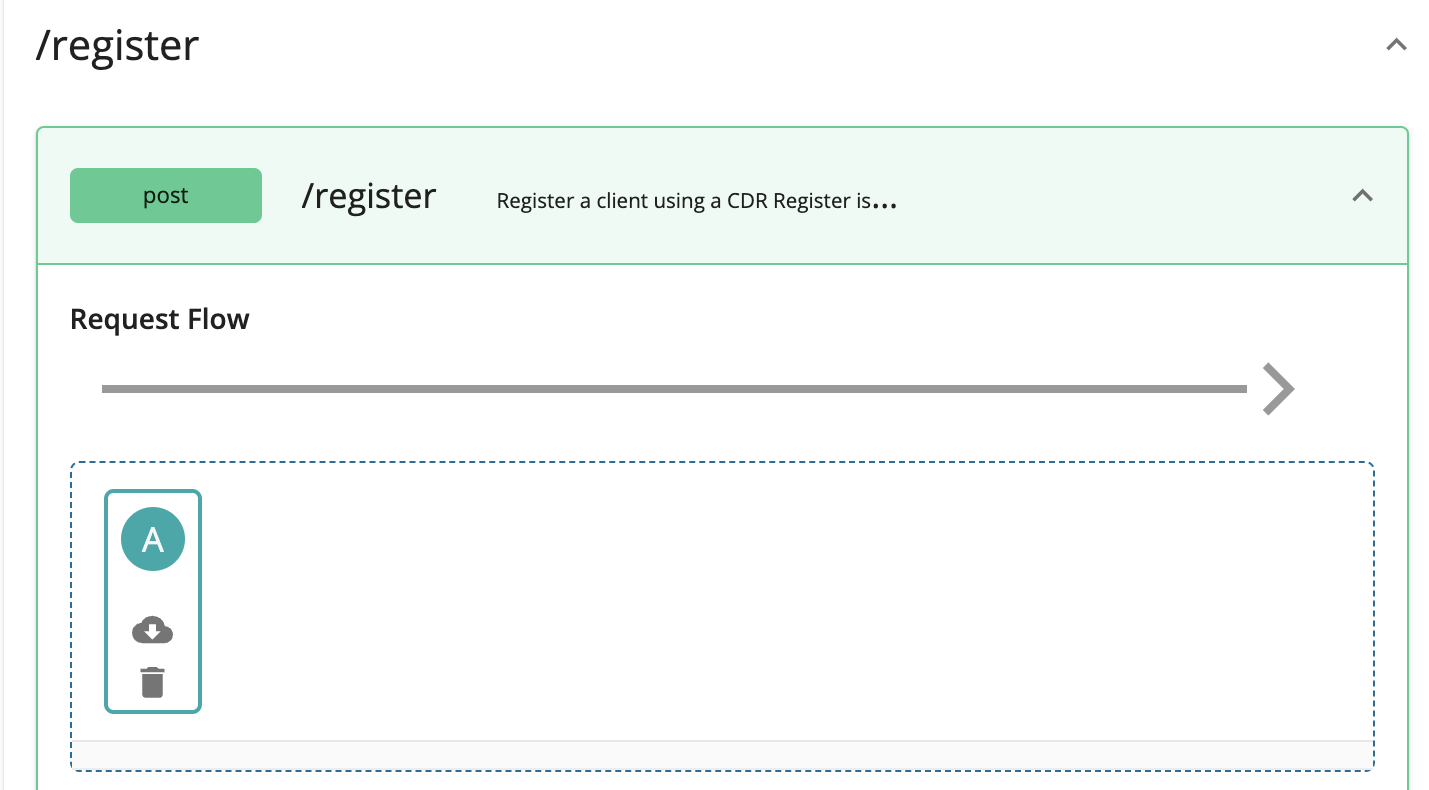
Expand the API endpoint you want from the list of API endpoints. For example:

-
Expand the HTTP method from the API endpoint you selected. For example:

-
Drag and drop the previously created policy to the Request Flow of the API endpoint.
-
Select Apply to all resources and click Save.
-
Scroll down and click Save.
-
-
Use the left menu panel and go to API Configurations > Endpoints.

-
Add a Dynamic Endpoint.

-
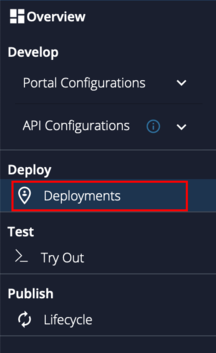
Go to Deployments using the left menu pane.
-
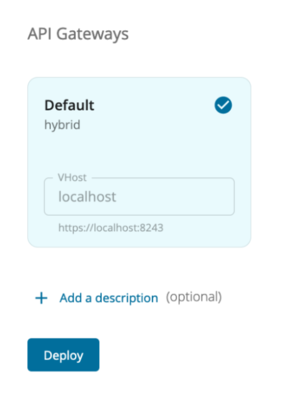
Select the API Gateway type, in this scenario, it is Default.
-
Click Deploy.
-
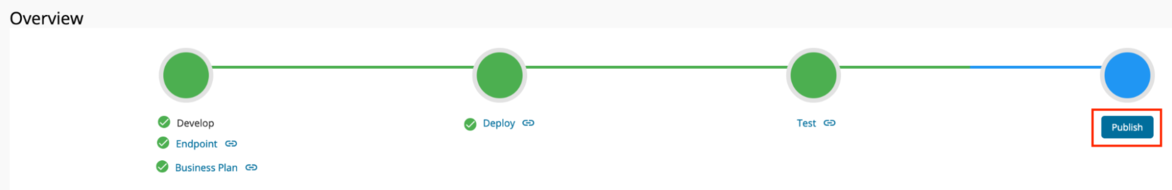
Go to Overview using the left menu pane.
-
Click Publish.
Summarized information for configuring APIs¶
Given below is a summary of configurations to follow when deploying the APIs in the toolkit.
| API | Swagger definition (yaml file) | Endpoint type | Message mediation (sequence file) |
|---|---|---|---|
| Account and Transaction API v3.1.11 | <APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/Accounts/3.1.11/account-info-openapi-3.1.11.yaml |
Dynamic Endpoint | <APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/Accounts/3.1.11/accounts-dynamic-endpoint-insequence-3.1.11.xml |
| Payment Initiation API v3.1.11 | <APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/Payments/3.1.11/payment-openapi-3.1.11.yaml |
Dynamic Endpoint | <APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/Payments/3.1.11/payments-dynamic-endpoint-insequence-3.1.11.xml |
| Confirmation of Funds API v3.1.11 | <APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/FundsConfirmation/3.1.11/funds-confirmation-openapi-3.1.11.yaml |
Dynamic Endpoint | <APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/FundsConfirmation/3.1.11/funds-confirmation-dynamic-endpoint-insequence-3.1.11.xml |
| Account and Transaction API v4.0.0 | <APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/Accounts/4.0.0/account-info-openapi-4.0.0.yaml |
Dynamic Endpoint | <APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/Accounts/4.0.0/accounts-dynamic-endpoint-insequence-4.0.0.xml |
| Payment Initiation API v4.0.0 | <APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/Payments/4.0.0/payment-openapi-4.0.0.yaml |
Dynamic Endpoint | <APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/Payments/4.0.0/payments-dynamic-endpoint-insequence-4.0.0.xml |
| Confirmation of Funds API v4.0.0 | <APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/FundsConfirmation/4.0.0/funds-confirmation-openapi-4.0.0.yaml |
Dynamic Endpoint | <APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/FundsConfirmation/4.0.0/funds-confirmation-dynamic-endpoint-insequence-4.0.0.xml |
| Dynamic Client Registration API v3.3.0 | <APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/DynamicClientRegistration/3.3.0/dynamic-client-registration-swagger.yaml |
Dynamic Endpoint | <APIM_HOME>/<OB_APIM_TOOLKIT_HOME>/repository/resources/apis/openbanking.org.uk/DynamicClientRegistration/3.3.0/dcr-dynamic-endpoint-insequence-3.3.0.xml |
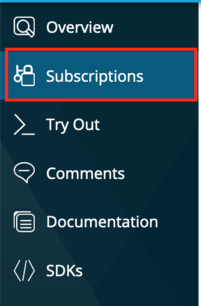
Subscribing to Account and Transaction API¶
-
The deployed API is now available in the Developer Portal at https://localhost:9443/devportal.
-
Select the AccountAndTransactionAPI V3.1 or AccountAndTransactionAPI V4.0 API.
-
Locate Subscriptions from the left menu pane.
-
From the Application dropdown, select the application that you want to be subscribed to the Account and Transaction API

-
Click Subscribe.
Invoking Account and Transaction API¶
Generating application access token¶
Once you register the application, generate an application access token.
- Generate the client assertion by signing the following JSON payload using supported algorithms.
Note
If you have configured the OB certificates,
-
Use the transport private key and transport public certificate for Transport layer security testing purposes.
-
Use the signing certificate and signing private keys for signing purposes.
{
"alg": "<The algorithm used for signing.>",
"kid": "<The thumbprint of the certificate.>",
"typ": "JWT"
}
{
"iss": "<This is the issuer of the token. For example, client ID of your application>",
"sub": "<This is the subject identifier of the issuer. For example, client ID of your application>",
"exp": <This is the epoch time of the token expiration date/time>,
"iat": <This is the epoch time of the token issuance date/time>,
"jti": "<This is an incremental unique value>",
"aud": "<This is the audience that the ID token is intended for. For example, https://<IS_HOST>:9446/oauth2/token>"
}
<signature: For DCR, the client assertion is signed by the private key of the signing certificate. For other scenarios, use the private signature of the application certificate.>eyJraWQiOiIyTUk5WFNLaTZkZHhDYldnMnJoRE50VWx4SmMiLCJhbGciOiJQUzI1NiJ9.eyJzdWIiOiJZRGNHNGY0OUcxM2tXZlZzbnFkaHo4Z2JhMndhIiwiYXVkIjoiaHR0cHM6Ly9sb2NhbGhvc3Q6OTQ0Ni9vYXV0aDIvdG9rZW4iLCJpc3MiOiJZRGNHNGY0OUcxM2tXZlZzbnFkaHo4Z2JhMndhIiwiZXhwIjoxNjI4Nzc0ODU1LCJpYXQiOjE2Mjg3NDQ4NTUsImp0aSI6IjE2Mjg3NDQ4NTUxOTQifQ.PkKRSDtkCyXabzLgGwAoy5C3jSORVU8X8sGDVrKpetPnjbCNx2wPlH-PzWUU1n05gdC7lDmoU21nsKLF_nE3iC-9hKEy4YsvJ7PFjNBPMOMUYDhRh9PCkPnec6f042zonb_ZifBq8r1aScUDoZ1L0hq7yjfZubwReFCWbESQ8PauuBuHRl7__kWvglthfgruQ7TTiIWiM60LWYct5TQWSF1IDcYGy03l-9OV5l260JBHPT4heLXzUQTarsh0PoWpv09xYLu8uGCexEt-HtRH8qwJGiFi5PiCA09_KyWVqbrcdjBloCmD5Kiqa1X0AnEbf9kKs0fqvcl7NN5-yVQUjg-
Run the following cURL command in a command prompt to generate the access token. Update the placeholders with relevant values.
curl -X POST \ https://localhost:9446/oauth2/token \ --cert <TRANSPORT_PUBLIC_KEY_FILE_PATH> --key <TRANSPORT_PRIVATE_KEY_FILE_PATH> \ -d 'grant_type=client_credentials&scope=accounts%20openid&client_assertion_type=urn:ietf:params:oauth:client-assertion-type:jwt-bearer&client_assertion=<CLIENT_ASSERTION_JWT>&redirect_uri=<REDIRECT_URI>&client_id=<CLIENT_ID>' -
Upon successful token generation, you can obtain a token as follows:
{ "access_token":"eyJ4NXQiOiJOVGRtWmpNNFpEazNOalkwWXpjNU1tWm1PRGd3TVRFM01XWXdOREU1TVdSbFpEZzROemM0WkEiLCJraWQiOiJNell4TW1Ga09HWXdNV0kwWldObU5EY3hOR1l3WW1NNFpUQTNNV0kyTkRBelpHUXpOR00wWkdSbE5qSmtPREZrWkRSaU9URmtNV0ZoTXpVMlpHVmxOZ19SUzI1NiIsImFsZyI6IlJTMjU2In0.eyJzdWIiOiJhZG1pbkB3c28yLmNvbUBjYXJib24uc3VwZXIiLCJhdXQiOiJBUFBMSUNBVElPTiIsImF1ZCI6IllEY0c0ZjQ5RzEza1dmVnNucWRoejhnYmEyd2EiLCJuYmYiOjE2Mjg3NDQ4NTYsImF6cCI6IllEY0c0ZjQ5RzEza1dmVnNucWRoejhnYmEyd2EiLCJzY29wZSI6ImFjY291bnRzIiwiaXNzIjoiaHR0cHM6XC9cL2xvY2FsaG9zdDo5NDQ2XC9vYXV0aDJcL3Rva2VuIiwiY25mIjp7Ing1dCNTMjU2IjoidllvVVlSU1E3Q2dvWXhOTVdXT3pDOHVOZlFyaXM0cFhRWDBabWl0Unh6cyJ9LCJleHAiOjE2Mjg3NDg0NTYsImlhdCI6MTYyODc0NDg1NiwianRpIjoiNzBjZDIzYzItMzYxZS00YTEwLWI4YTQtNzg2MTljZmQ2MWJmIn0.WT9d2ov9kfSe75Q6ia_VNvJ12lNkrkMZNWdHu_Ata_nEpM8AWj4Mtc0e8Yb0oZFif_ypNgBtE2ck29nQLFgQ1IicL_OMIFUuwykro2oOCcFAbz7o_rhGsh39aW-ORlxm11_csmNeaWZNfC7lPp-9hBmNt9Sons_pCm2beTMFreZQyywPrJoQ9vwt1QCmkAlTP33YnPrf0u0RQePQvUq81RiJiokhZvwVufHARZv8KLtS8VLrpfbEoSglON_XkumydVjvRWs17I3Ot9zUj6kndHBsqMPZdq_aNQHntftdSI7TVNj5f66Q_4Uafz_hMXADS46pw87rTgzENHHf-5SRhw", "scope":"accounts", "token_type":"Bearer", "expires_in":3600 }
Initiating an account consent¶
In this step, the AISP generates a request to get the consent of the PSU to access the accounts and banking information.
- Create an account consent using the following request format:
curl -X POST \
https://localhost:8243/open-banking/v3.1/aisp/account-access-consents \
-H 'Authorization: Bearer <APPLICATION_ACCESS_TOKEN>' \
-H 'Content-Type: application/json' \
-H 'Accept: application/json' \
--cert <TRANSPORT_PUBLIC_KEY_FILE_PATH> --key <TRANSPORT_PRIVATE_KEY_FILE_PATH> \
-d '{
"Data":{
"Permissions":[
"ReadAccountsBasic",
"ReadAccountsDetail",
"ReadBalances",
"ReadBeneficiariesBasic",
"ReadBeneficiariesDetail",
"ReadDirectDebits",
"ReadProducts",
"ReadStandingOrdersBasic",
"ReadStandingOrdersDetail",
"ReadTransactionsBasic",
"ReadTransactionsCredits",
"ReadTransactionsDebits",
"ReadTransactionsDetail",
"ReadStatementsBasic",
"ReadStatementsDetail",
"ReadOffers",
"ReadParty",
"ReadPartyPSU",
"ReadScheduledPaymentsBasic",
"ReadScheduledPaymentsDetail",
"ReadPAN"
],
"ExpirationDateTime":"2022-01-30T10:29:08.814+05:30",
"TransactionFromDateTime":"2022-01-25T10:29:08.824+05:30",
"TransactionToDateTime":"2022-01-28T10:29:08.824+05:30"
},
"Risk":{
}
}'curl -X POST \
https://localhost:8243/open-banking/v4.0 /aisp/account-access-consents \
-H 'Authorization: Bearer <APPLICATION_ACCESS_TOKEN>' \
-H 'Content-Type: application/json' \
-H 'Accept: application/json' \
--cert <TRANSPORT_PUBLIC_KEY_FILE_PATH> --key <TRANSPORT_PRIVATE_KEY_FILE_PATH> \
-d '{
"Data":{
"Permissions":[
"ReadAccountsBasic",
"ReadAccountsDetail",
"ReadBalances",
"ReadBeneficiariesBasic",
"ReadBeneficiariesDetail",
"ReadDirectDebits",
"ReadProducts",
"ReadStandingOrdersBasic",
"ReadStandingOrdersDetail",
"ReadTransactionsBasic",
"ReadTransactionsCredits",
"ReadTransactionsDebits",
"ReadTransactionsDetail",
"ReadStatementsBasic",
"ReadStatementsDetail",
"ReadOffers",
"ReadParty",
"ReadPartyPSU",
"ReadScheduledPaymentsBasic",
"ReadScheduledPaymentsDetail",
"ReadPAN"
],
"ExpirationDateTime":"2022-01-30T10:29:08.814+05:30",
"TransactionFromDateTime":"2022-01-25T10:29:08.824+05:30",
"TransactionToDateTime":"2022-01-28T10:29:08.824+05:30"
},
"Risk":{
}
}'-
The response contains a Consent Id. A sample response is as follows:
{ "Data":{ "Status":"AwaitingAuthorisation", "StatusUpdateDateTime":"2022-01-25T10:29:23+05:30", "CreationDateTime":"2022-01-25T10:29:23+05:30", "TransactionToDateTime":"2022-01-28T10:29:08.824+05:30", "ExpirationDateTime":"2022-01-30T10:29:08.814+05:30", "Permissions":[ "ReadAccountsBasic", "ReadAccountsDetail", "ReadBalances", "ReadBeneficiariesBasic", "ReadBeneficiariesDetail", "ReadDirectDebits", "ReadProducts", "ReadStandingOrdersBasic", "ReadStandingOrdersDetail", "ReadTransactionsBasic", "ReadTransactionsCredits", "ReadTransactionsDebits", "ReadTransactionsDetail", "ReadStatementsBasic", "ReadStatementsDetail", "ReadOffers", "ReadParty", "ReadPartyPSU", "ReadScheduledPaymentsBasic", "ReadScheduledPaymentsDetail", "ReadPAN" ], "ConsentId":"343eea20-3f9d-4c12-8777-fe446c554210", "TransactionFromDateTime":"2022-01-25T10:29:08.824+05:30" }, "Links":{ "Self":"https://localhost:8243/open-banking/3.1/aisp/account-access-consents/343eea20-3f9d-4c12-8777-fe446c554210" }, "Meta":{ }, "Risk":{ } }{ "Data":{ "Status":"AWAU", "StatusUpdateDateTime":"2022-01-25T10:29:23+05:30", "CreationDateTime":"2022-01-25T10:29:23+05:30", "TransactionToDateTime":"2022-01-28T10:29:08.824+05:30", "ExpirationDateTime":"2022-01-30T10:29:08.814+05:30", "Permissions":[ "ReadAccountsBasic", "ReadAccountsDetail", "ReadBalances", "ReadBeneficiariesBasic", "ReadBeneficiariesDetail", "ReadDirectDebits", "ReadProducts", "ReadStandingOrdersBasic", "ReadStandingOrdersDetail", "ReadTransactionsBasic", "ReadTransactionsCredits", "ReadTransactionsDebits", "ReadTransactionsDetail", "ReadStatementsBasic", "ReadStatementsDetail", "ReadOffers", "ReadParty", "ReadPartyPSU", "ReadScheduledPaymentsBasic", "ReadScheduledPaymentsDetail", "ReadPAN" ], "ConsentId":"343eea20-3f9d-4c12-8777-fe446c554210", "TransactionFromDateTime":"2022-01-25T10:29:08.824+05:30" }, "Links":{ "Self":"https://localhost:8243/open-banking/4.0/aisp/account-access-consents/343eea20-3f9d-4c12-8777-fe446c554210" }, "Meta":{ }, "Risk":{ } }
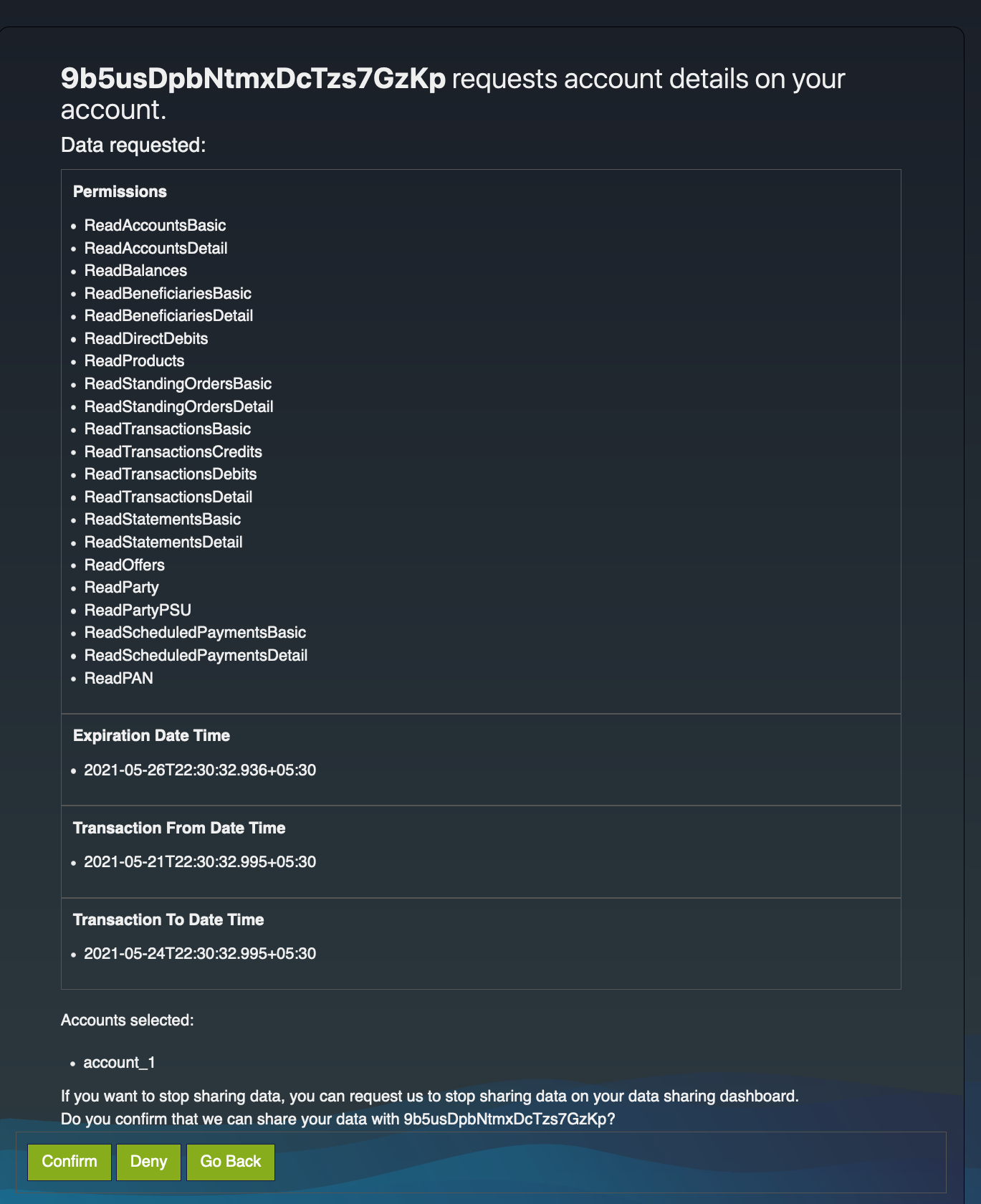
Authorizing a consent¶
The AISP application redirects the bank customer to authenticate and approve/deny application-provided consents.
-
Generate the request object by signing the following JSON payload using supported algorithms.
{ "kid": "<CERTIFICATE_FINGERPRINT>", "alg": "<SUPPORTED_ALGORITHM>", "typ": "JWT" } { "max_age": 86400, "aud": "<This is the audience that the ID token is intended for. e.g., https://<IS_HOST>:9446/oauth2/token>", "scope": "accounts openid", "iss": "<APPLICATION_ID>", "claims": { "id_token": { "acr": { "values": [ "urn:openbanking:psd2:sca", "urn:openbanking:psd2:ca" ], "essential": true }, "openbanking_intent_id": { "value": "<CONSENTID>", "essential": true } }, "userinfo": { "openbanking_intent_id": { "value": "<CONSENTID>", "essential": true } } }, "response_type": "<code:Retrieves authorize code/code id_token: Retrieves authorize token and ID token>", "redirect_uri": "<CLIENT_APPLICATION_REDIRECT_URI>", "state": "YWlzcDozMTQ2", "exp": <EPOCH_TIME_OF_TOKEN_EXPIRATION>, "nonce": "<PREVENTS_REPLAY_ATTACKS>", "client_id": "<APPLICATION_ID>" }eyJraWQiOiIyTUk5WFNLaTZkZHhDYldnMnJoRE50VWx4SmMiLCJhbGciOiJQUzI1NiIsInR5cCI6IkpXVCJ9.eyJtYXhfYWdlIjo4NjQwMCwiYXVkIjoiaHR0cHM6Ly9sb2NhbGhvc3Q6OTQ0Ni9vYXV0aDIvdG9rZW4iLCJzY29wZSI6ImFjY291bnRzIG9wZW5pZCIsImlzcyI6IllEY0c0ZjQ5RzEza1dmVnNucWRoejhnYmEyd2EiLCJjbGFpbXMiOnsiaWRfdG9rZW4iOnsiYWNyIjp7InZhbHVlcyI6WyJ1cm46b3BlbmJhbmtpbmc6cHNkMjpzY2EiLCJ1cm46b3BlbmJhbmtpbmc6cHNkMjpjYSJdLCJlc3NlbnRpYWwiOnRydWV9LCJvcGVuYmFua2luZ19pbnRlbnRfaWQiOnsidmFsdWUiOiJkYzY0ZTI3Yy03MTM5LTQ0MGUtOGI0Zi1jZDcwYzY0OWUwOTYiLCJlc3NlbnRpYWwiOnRydWV9fSwidXNlcmluZm8iOnsib3BlbmJhbmtpbmdfaW50ZW50X2lkIjp7InZhbHVlIjoiZGM2NGUyN2MtNzEzOS00NDBlLThiNGYtY2Q3MGM2NDllMDk2IiwiZXNzZW50aWFsIjp0cnVlfX19LCJyZXNwb25zZV90eXBlIjoiY29kZSBpZF90b2tlbiIsInJlZGlyZWN0X3VyaSI6Imh0dHBzOi8vd3NvMi5jb20iLCJzdGF0ZSI6IllXbHpjRG96TVRRMiIsImV4cCI6MTYzMzU4NjQwOCwibm9uY2UiOiJuLTBTNl9XekEyTWoiLCJjbGllbnRfaWQiOiJZRGNHNGY0OUcxM2tXZlZzbnFkaHo4Z2JhMndhIn0.OK0G0hxKQwBYEV8G9cDZAMkuLYU0Go3O8DhphzlYXpaTxPTpNUGFuUk6wiDNh0SGt-bBg6lC0mv7FrfBMv9r79yuDME6iqefgVB3PXhqWfGfRvhDY0wW9HvfGsWdrJ3MUxV0RomZeEyoooD3TrRItsc8-CsmAz5_BbCgSwYRGMcAwS89P-twlc3CE7YYru1ktGkoVQ8UvQA8IiXoomq-eS3oebRTD8DmYkjpeKURkO0rrssMuxOcN64GcgEAQeDW_dANSq_YSX9yTGGFWIzVmkafT5qzz0792VIGDtxx5Tr7keuDWIR_2SBdo_49oVLHttLu_kwNhN9u-Ed2Hx1wPQ -
The ASPSP sends the request to the customer stating the accounts and information that the API consumer wishes to access. This request is in the format of a URL as follows.
Update the placeholders with relevant values and run the following in a browser to prompt the invocation of the authorize API.
https://<IS_HOST>:9446/oauth2/authorize?response_type=code%20id_token&client_id=<CLIENT_ID>&scope=accounts%20op enid&redirect_uri=<APPLICATION_REDIRECT_URI>&state=YWlzcDozMTQ2&request=<REQUEST_OBJECT>&prompt=login&nonce=<REQUEST_OBJECT_NONCE> -
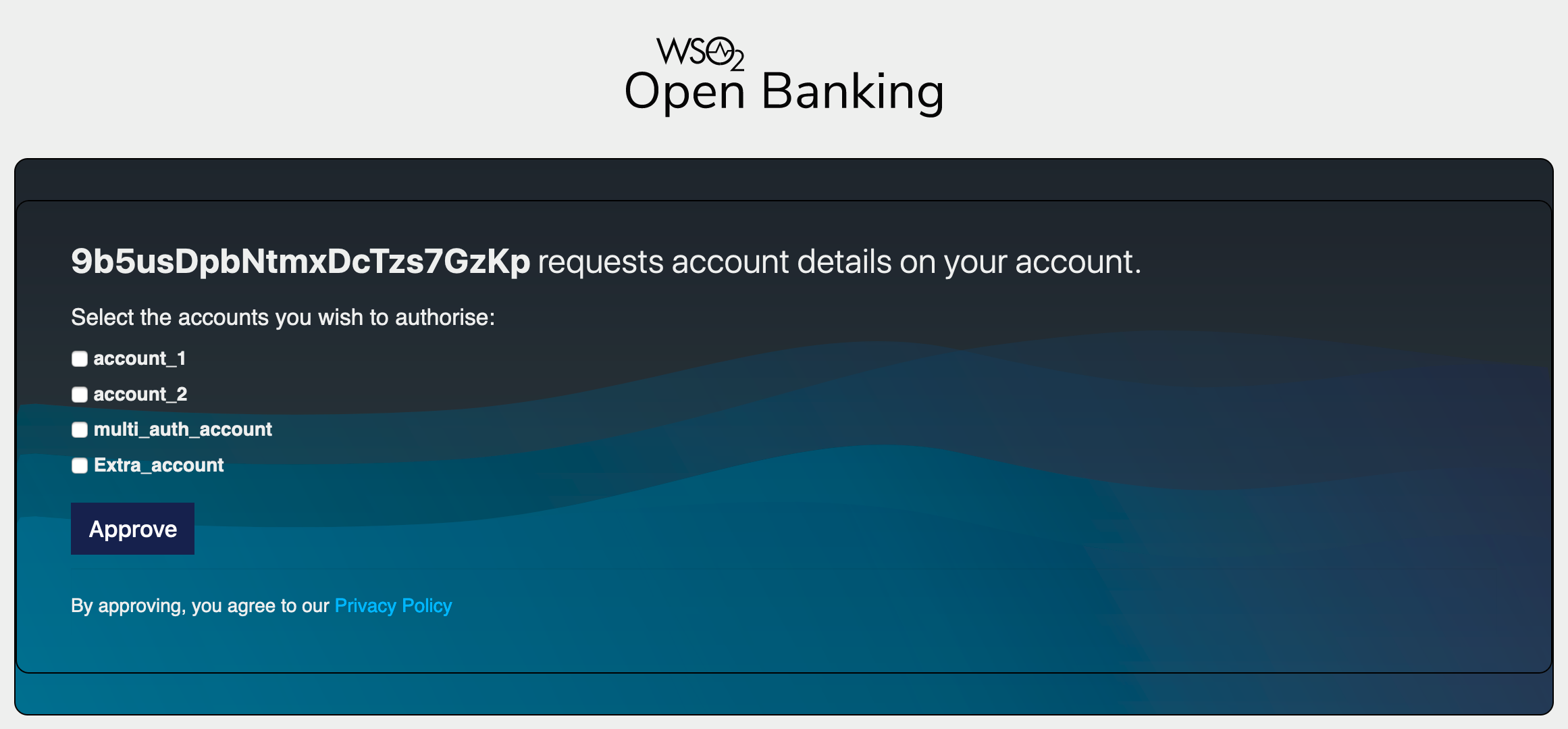
Upon successful authentication, the user is redirected to the consent authorize page. Use the login credentials of a user that has a
subscriberrole. -
The page displays the data requested by the consent such as permissions, transaction period, and expiration date.
-
At the bottom of the page, a list of bank accounts that the AISP wishes to access is displayed.
-
Select one or more accounts from the list and click Confirm.
-
Upon providing consent, an authorization code is generated on the web page of the redirect_uri. See the sample given below:
https://wso2.com/#code=5591c5a0-14d0-3ca9-bec2-c1efe86e32ce&id_token=eyJ4NXQiOiJOVGRtWmpNNFpEazNOalkwWXpjNU1tWm1PRGd3TVRFM01XWXdOREU1TVdSbFpEZzROemM0WkEiLCJraWQiOiJNell4TW1Ga09HWXdNV0kwWldObU5EY3hOR1l3WW1NNFpUQTNNV0kyTkRBelpHUXpOR00wWkdSbE5qSmtPREZrWkRSaU9URmtNV0ZoTXpVMlpHVmxOZ19SUzI1NiIsImFsZyI6IlJTMjU2In0.eyJhdF9oYXNoIjoiWC14OFhwV2I3cGIyYnU2NHVLYktTUSIsInN1YiI6ImFkbWluQHdzbzIuY29tQGNhcmJvbi5zdXBlciIsImFtciI6WyJCYXNpY0F1dGhlbnRpY2F0b3IiXSwiaXNzIjoiaHR0cHM6XC9cL2xvY2FsaG9zdDo5NDQ2XC9vYXV0aDJcL3Rva2VuIiwibm9uY2UiOiJuLTBTNl9XekEyTSIsInNpZCI6ImM5MDViNmFhLTBiNWEtNGM4Ni04NWYzLTk0MTI5YWRlMTVjNiIsImF1ZCI6IllEY0c0ZjQ5RzEza1dmVnNucWRoejhnYmEyd2EiLCJjX2hhc2giOiJ5Y3lhNHBBN2ZfSW9uQzlpaWl1TnZ3Iiwib3BlbmJhbmtpbmdfaW50ZW50X2lkIjoiNjFmOWEzNTctNDE2MC00OGE2LTg0NWMtYzM3ZjEwN2ZlNjQ4Iiwic19oYXNoIjoiMWNIaVdBMVN2NmpKc0t6SDRFbnk1QT09XHJcbiIsImF6cCI6IllEY0c0ZjQ5RzEza1dmVnNucWRoejhnYmEyd2EiLCJleHAiOjE2Mjg3NTMxODIsImlhdCI6MTYyODc0OTU4Mn0.mGgNWc12T8a5pW6QQRF6RXoVci0ToHLCttLiCGY6KraHMzGmRFUm6jz6Clbxk_447DdoKONAqY_2uCQCRkudjMk_7sTCV-DxOIbFYctrTiU01CvjKLbNcr8tjHaaIp8rhft1K0q3h0kVxyRoo3A1WQDBJFpp2jWqqJMyjShzEf6bbojtpBw2kyAazInhnm4XFSYchGPDF7XP-vRwCHNG532dg0kXvUrdA9B7RQGnQlay296rN1pRN-GTnC6_io_anf6a5Q3ovuaxcODnbb540hnjty3scPISj38La21iQTWEBTGlBUPnXs10pXjzCmib5wng37rXV8PDslbMfRqMhg&state=YWlzcDozMTQ2&session_state=507a0e617fe39feae18795b746c09fc44dd7e8658348a6c1ce2e91778224a5a4.IFBUQh0silRELhJocuhouw
The authorization code from the below URL is in the code parameter (code=5591c5a0-14d0-3ca9-bec2-c1efe86e32ce).
Generating user access token¶
In this section, you will be generating an access token using the authorization code generated in the section above.
-
Generate the client assertion by signing the following JSON payload using supported algorithms.
Note
If you have configured the OB certificates,
-
Use the transport private key and transport public certificate for Transport layer security testing purposes.
-
Use the signing certificate and signing private keys for signing purposes.
Format: { "alg": "<The algorithm used for signing.>", "kid": "<The thumbprint of the certificate.>", "typ": "JWT" } { "iss": "<This is the issuer of the token. For example, client ID of your application>", "sub": "<This is the subject identifier of the issuer. For example, client ID of your application>", "exp": <This is the epoch time of the token expiration date/time>, "iat": <This is the epoch time of the token issuance date/time>, "jti": "<This is an incremental unique value>", "aud": "<This is the audience that the ID token is intended for. For example, https://<IS_HOST>:9446/oauth2/token>" } <signature: For DCR, the client assertion is signed by the private key of the signing certificate. Otherwise, the private signature of the application certificate is used.>eyJraWQiOiIyTUk5WFNLaTZkZHhDYldnMnJoRE50VWx4SmMiLCJhbGciOiJQUzI1NiJ9.eyJzdWIiOiJZRGNHNGY0OUcxM2tXZlZzbnFkaHo4Z2JhMndhIiwiYXVkIjoiaHR0cHM6Ly9sb2NhbGhvc3Q6OTQ0Ni9vYXV0aDIvdG9rZW4iLCJpc3MiOiJZRGNHNGY0OUcxM2tXZlZzbnFkaHo4Z2JhMndhIiwiZXhwIjoxNjI4Nzc0ODU1LCJpYXQiOjE2Mjg3NDQ4NTUsImp0aSI6IjE2Mjg3NDQ4NTUxOTQifQ.PkKRSDtkCyXabzLgGwAoy5C3jSORVU8X8sGDVrKpetPnjbCNx2wPlH-PzWUU1n05gdC7lDmoU21nsKLF_nE3iC-9hKEy4YsvJ7PFjNBPMOMUYDhRh9PCkPnec6f042zonb_ZifBq8r1aScUDoZ1L0hq7yjfZubwReFCWbESQ8PauuBuHRl7__kWvglthfgruQ7TTiIWiM60LWYct5TQWSF1IDcYGy03l-9OV5l260JBHPT4heLXzUQTarsh0PoWpv09xYLu8uGCexEt-HtRH8qwJGiFi5PiCA09_KyWVqbrcdjBloCmD5Kiqa1X0AnEbf9kKs0fqvcl7NN5-yVQUjg -
-
Run the following cURL command in a command prompt to generate the access token. Update the placeholders with relevant values.
curl -X POST \ https://localhost:9446/oauth2/token \ -H 'Cache-Control: no-cache' \ -H 'Content-Type: application/x-www-form-urlencoded' \ --cert <PUBLIC_KEY_FILE_PATH> --key <PRIVATE_KEY_FILE_PATH> \ -d 'grant_type=authorization_code&client_assertion_type=urn%3Aietf%3Aparams%3Aoauth%3Aclient-assertion-type%3Ajwt-bearer&client_assertion=<CLIENT_ASSERTION>&code=<CODE_FROM_ABOVE_STEP>&scope=openid%20accounts&redirect_uri=<REDIRECT_URI>' -
Upon successful token generation, you can obtain a token as follows:
{ "access_token": "eyJ4NXQiOiJOVGRtWmpNNFpEazNOalkwWXpjNU1tWm1PRGd3TVRFM01XWXdOREU1TVdSbFpEZzROemM0WkEiLCJraWQiOiJNell4TW1Ga09HWXdNV0kwWldObU5EY3hOR1l3WW1NNFpUQTNNV0kyTkRBelpHUXpOR00wWkdSbE5qSmtPREZrWkRSaU9URmtNV0ZoTXpVMlpHVmxOZ19SUzI1NiIsImFsZyI6IlJTMjU2In0.eyJzdWIiOiJhZG1pbkB3c28yLmNvbUBjYXJib24uc3VwZXIiLCJhdXQiOiJBUFBMSUNBVElPTl9VU0VSIiwiYXVkIjoiWURjRzRmNDlHMTNrV2ZWc25xZGh6OGdiYTJ3YSIsIm5iZiI6MTYyODc0NjU5MiwiYXpwIjoiWURjRzRmNDlHMTNrV2ZWc25xZGh6OGdiYTJ3YSIsInNjb3BlIjoiYWNjb3VudHMgY29uc2VudF9pZGRjNjRlMjdjLTcxMzktNDQwZS04YjRmLWNkNzBjNjQ5ZTA5NiBvcGVuaWQiLCJpc3MiOiJodHRwczpcL1wvbG9jYWxob3N0Ojk0NDZcL29hdXRoMlwvdG9rZW4iLCJjbmYiOnsieDV0I1MyNTYiOiJ2WW9VWVJTUTdDZ29ZeE5NV1dPekM4dU5mUXJpczRwWFFYMFptaXRSeHpzIn0sImV4cCI6MTYyODc1MDE5MiwiaWF0IjoxNjI4NzQ2NTkyLCJqdGkiOiI3NTA4MmEzYS1iNDllLTRjZjEtYjI4Ni1lMWJiYTYwZTViNTYiLCJjb25zZW50X2lkIjoiZGM2NGUyN2MtNzEzOS00NDBlLThiNGYtY2Q3MGM2NDllMDk2In0.MhNpi0C2vASqrigTE1qGjK_7PY722H4PjzOSwMKcmFo7YgIFIBQdtj2BRJN0y7WAOFYGqh5lUFKMJWrXXtOyo0-6pWheluQfmOMiTyqOzA7WcTZAwYUzeoRmgWtR_LCYNwzm1O7CcNeavLGucLkCmpTW9Xvn3dKkk0XFonzrrCH9QqMrA0iQP6vYgH5wH4rDxcK_6Vk1r0X33sHVM-k4ifbcIzZekUdJIgNQfK1Qosslmvm1LZfEZ1vi63cfkc0IexNW6jJYvvZxdYJVz42EKKIqR_Z_HBs8umamqhUqKAkcv7Q76bNNPpM1iBJK-eDVf8yfIr9243fyictuqhP-2Q", "refresh_token": "98dfa00b-a2a4-3ba0-9af2-4fac26f317b3", "scope": "accounts openid", "id_token": "eyJ4NXQiOiJOVGRtWmpNNFpEazNOalkwWXpjNU1tWm1PRGd3TVRFM01XWXdOREU1TVdSbFpEZzROemM0WkEiLCJraWQiOiJNell4TW1Ga09HWXdNV0kwWldObU5EY3hOR1l3WW1NNFpUQTNNV0kyTkRBelpHUXpOR00wWkdSbE5qSmtPREZrWkRSaU9URmtNV0ZoTXpVMlpHVmxOZ19SUzI1NiIsImFsZyI6IlJTMjU2In0.eyJhdF9oYXNoIjoiUEFGdl9WZFdqREp0bFYyN1U1NEJYdyIsImF1ZCI6IllEY0c0ZjQ5RzEza1dmVnNucWRoejhnYmEyd2EiLCJjX2hhc2giOiJac2l4aVM4c2RBZFJhVHVHZjlYbmxBIiwic3ViIjoiYWRtaW5Ad3NvMi5jb21AY2FyYm9uLnN1cGVyIiwibmJmIjoxNjI4NzQ2NTkyLCJhenAiOiJZRGNHNGY0OUcxM2tXZlZzbnFkaHo4Z2JhMndhIiwiYW1yIjpbIkJhc2ljQXV0aGVudGljYXRvciJdLCJpc3MiOiJodHRwczpcL1wvbG9jYWxob3N0Ojk0NDZcL29hdXRoMlwvdG9rZW4iLCJleHAiOjE2Mjg3NTAxOTIsImlhdCI6MTYyODc0NjU5Miwibm9uY2UiOiJuLTBTNl9XekEyTSJ9.VRMfZouZTRm0QotoN0g95QjH7qKG_KwLExJyyb6AGbFewulyjwyPTJsHIj7D19ZZuNL14KqdCw51X3QjDXjLuvE6oas12EpKwHBuAAJjRtLf7NbbRPFok8Qlq011U_qNfYgcFubOQ5bXTr1QpwIU8imExvRxYS5UzsGyvluQ9hzjmRZM5cfwJ7hck71joX45Ue3E2tIvWxqyU13EJOyD3gd2QuhM6GSq3oWk8S0N_y7ACWLEHM8nzBUXiRo03D4DIacnmiZeicjIiim-SzF70tDJe70qy_nqbgf6VGqdAAIXyMXAvKxF5QWwYd5seMvt5o-_hCsI6DV69FawGJcbVQ", "token_type": "Bearer", "expires_in": 3600 }
Invoking Accounts and Transaction API¶
Once the PSU approves the account consent, the AISP is eligible to access the account details of the PSU.
The AISP can now invoke the GET/ accounts endpoint available in the Account and Transaction API. This retrieves a full list of accounts that the PSU has authorised the AISP to access. The Account Ids returned are used to retrieve other resources for a specific AccountId.
-
A sample request looks as follows:
curl -X GET \ https://localhost:8243/open-banking/v3.1/aisp/accounts' \ -H 'x-fapi-financial-id: open-bank' \ -H 'Authorization: Bearer <USER_ACCESS_TOKEN>' \ -H 'Accept: application/json' \ -H 'charset: UTF-8' \ -H 'Content-Type: application/json; charset=UTF-8' --cert <PUBLIC_KEY_FILE_PATH> --key <PRIVATE_KEY_FILE_PATH> \curl -X GET \ https://localhost:8243/open-banking/v4.0/aisp/accounts' \ -H 'x-fapi-financial-id: open-bank' \ -H 'Authorization: Bearer <USER_ACCESS_TOKEN>' \ -H 'Accept: application/json' \ -H 'charset: UTF-8' \ -H 'Content-Type: application/json; charset=UTF-8' --cert <PUBLIC_KEY_FILE_PATH> --key <PRIVATE_KEY_FILE_PATH> \ -
The request retrieves the account information for all the accounts related to the PSU. Given below is a sample response:
{ "Data":{ "Account":[ { "AccountId":"30080012343456", "Status":"Enabled", "StatusUpdateDateTime":"2020-04-16T06:06:06+00:00", "Currency":"GBP", "AccountType":"Personal", "AccountSubType":"CurrentAccount", "Nickname":"Bills", "OpeningDate":"2020-01-16T06:06:06+00:00", "MaturityDate":"2025-04-16T06:06:06+00:00", "Account":[ { "SchemeName":"SortCodeAccountNumber", "Identification":"30080012343456", "Name":"Alex Karter", "SecondaryIdentification":"00021" } ] } ] }, "Links":{ "Self":"https://api.alphabank.com/open-banking/v3.0/accounts" }, "Meta":{ "TotalPages":1 } }{ "Data":{ "Account":[ { "AccountId": "30080012343456", "Status": "Enabled", "StatusUpdateDateTime": "2020-04-16T06:06:06+00:00", "Currency": "GBP", "AccountCategory": "Personal", "AccountTypeCode": "CACC", "Nickname": "Bills", "OpeningDate": "2020-01-16T06:06:06+00:00", "MaturityDate": "2025-04-16T06:06:06+00:00", "Account": [ { "SchemeName": "CLAV", "Identification": "30080012343456", "Name": "Mr Kevin", "SecondaryIdentification": "00021" } ] } ] }, "Links":{ "Self":"https://api.alphabank.com/open-banking/v3.0/accounts" }, "Meta":{ "TotalPages":1 } }